TEE Compile
Background
In the current technological landscape, there's a glaring absence of mechanisms to verify that an executable file has been compiled from a specific source code. This gap poses significant challenges in terms of security, transparency, and trust, as there is no definitive way to prove the authenticity of the compiled software.
To address this issue, we are introducing a method that involves standardizing the compilation process within an enclave environment. An enclave is a protected, isolated area of execution, where code can be run in confidentiality and integrity, safeguarded from potential tampering or unauthorized access.
Workflow
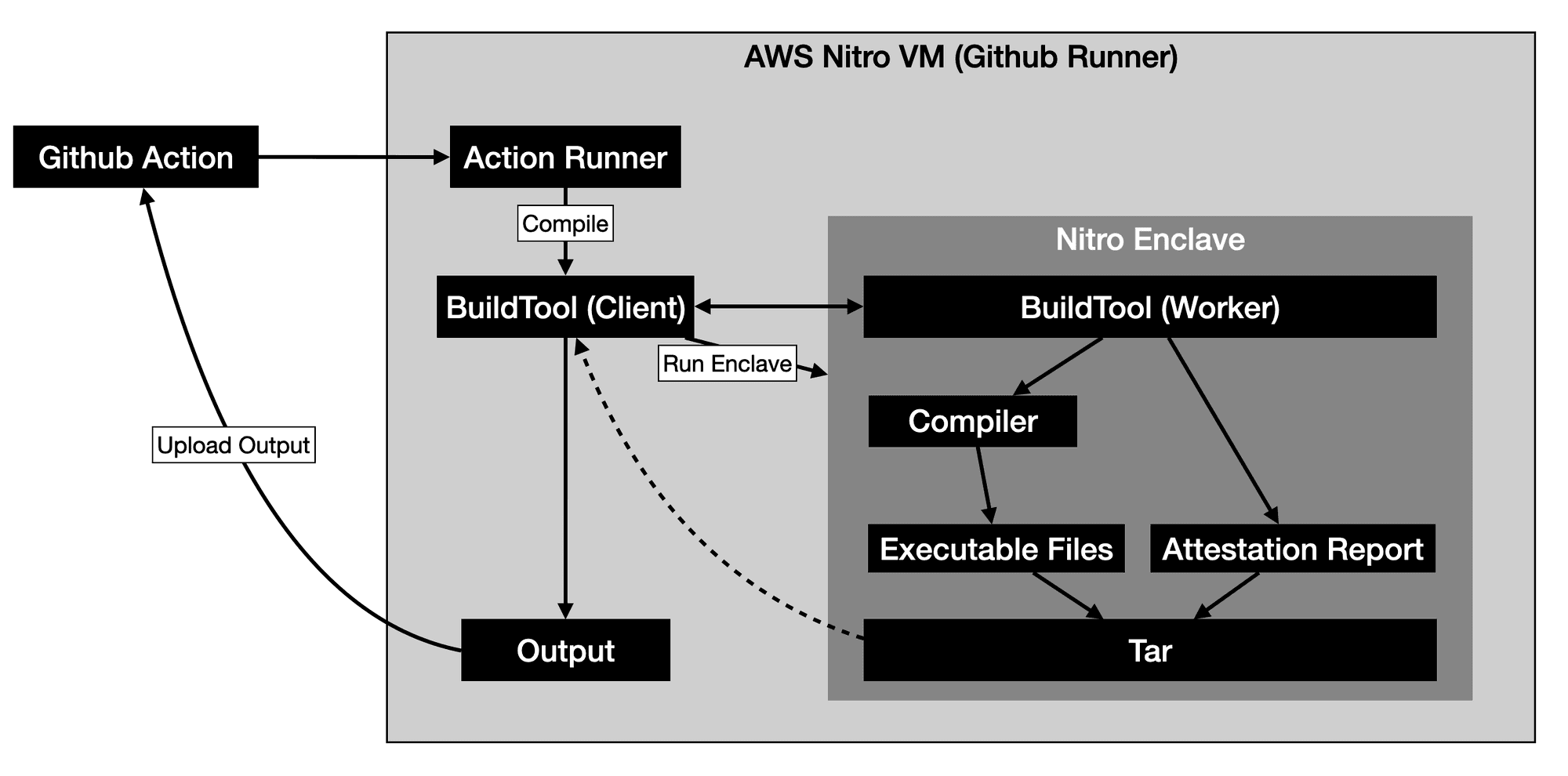
Roles:
- Action Runner:
- TEE Compile:
- Responsible for compiling the source code into executable files.
- Divided into Client and Worker two parts, the Client is responsible for running Enclave. Since the enclave cannot directly communicate with the outside, this part of the work is done through communication between Worker and Client.
- Client will submit the source code to Worker, and the Worker is responsible for collecting relevant information, and then compiling, finally generating the Executable Files, and returning them to the Client.
- Client will save the Executable Files locally.
Initialization Work
-
The Project Owner is responsible for running an Aws Nitro VM and initializing it, including configuring it as a GitHub Action Runner and installing TEE Compile.
-
Download the corresponding language's enclave image (.eif) from a trusted source.
- Different languages and different compiler versions will have different images.
-
Create a build.json in the project root directory, for example:
{ "language": "rust", "input": { "cmd": "cargo build" }, "output": { "files": [ "target/debug/rust-project" ] } }
New Version Release
- Trigger
BuildTool(Client)in the runner through GitHub Action for compilation. - The Action Runner will download the code, and execute the
BuildTool(Client),then scan the configuration files in the project, using an enclave image base on the project configuration. BuildTool(Worker)will obtain the code via Builder, understanding from the configuration files how to compile the project (language, compilation commands to be executed, information to be collected, and list of output files).BuildTool(Worker)will execute the compilation program, hijacking network traffic in a specific wayBuildTool(Worker)will collect the produced files, calculate the hash, and generate an Attestation Report (containing information about input and output).- Package the Executable Files and Attestation Report into a tar file, outputting through
BuildTool(Worker)to the outside world, such as GitHub, and ultimately provide to Project User.
Report Verification
- Whether the hash of the produced executable files is the same.
- Whether the compiled image is known to be trustworthy.
- Verify the issuer of the report.
Challenges
- The attestor can recreate the compilation environment according to the Attestation Report, thus verifying.
- The majority of votes wins.